Cyber criminals have secretly hijacked more than 14,000 devices worldwide in order to carry out attacks that are almost impossible to protect against, security researchers have warned.
The majority of devices infected by the sophisticated new malware, dubbed ‘KadNap’, are Asus routers, which are being used to route malicious traffic to carry out large-scale cyber attacks.
Details of the KadNap botnet were shared by the cyber security firm Lumen in a new report, which revealed that it is using a decentralised peer-to-peer system to avoid network detection.
A botnet is created by compromising the security of internet-connected devices, which can range from routers to smart fridges.
These devices are then covertly hijacked and linked together to carry out distributed-denial-of-service (DDoS) attacks, which overwhelms websites and online services with traffic to knock them offline.
“As modern society increasingly relies on internet-exposed Internet of Things (IoT) devices, the opportunities for malicious actors to exploit vulnerabilities continue to abound,” Lumen’s report stated.
“Threat actors are building large-scale botnets specifically designed to hijack devices in this growing pool of targets, using them to route traffic and evade detection by network security systems.”
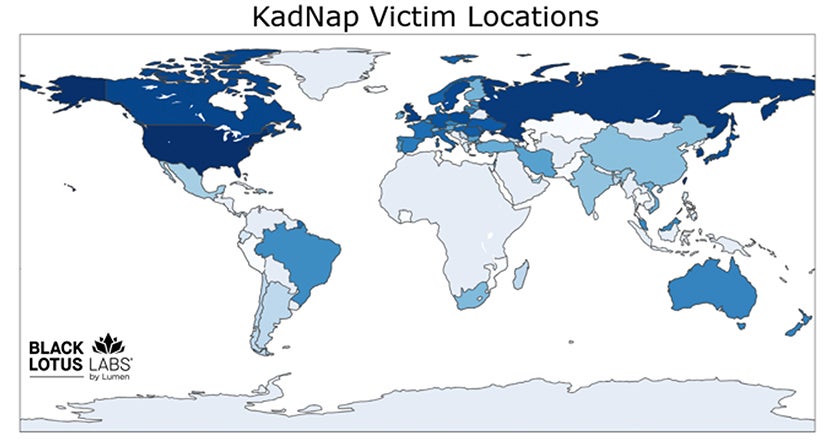
The majority of KadNap victims are located in the US, though security researchers have identified infected devices in the UK, Australia, Brazil, Russia, and across Europe.
For the average owner of an Asus router infected with KadNap, the malware would be undetectable beyond internet speeds feeling slightly sluggish at times.
Award-winning security software you can trust. Always.
Get All-in-One Protection for Your Digital Life.
LEARN MORE
ADVERTISEMENT
Award-winning security software you can trust. Always.
Get All-in-One Protection for Your Digital Life.
LEARN MORE
ADVERTISEMENT
Its decentralised design means there is no central server that could be easily shut down by law enforcement, making the KadNap botnet incredibly resilient to attempts to dismantle it.
Using traffic from household routers means the attackers can bypass conventional security filters, as it looks like the traffic is coming from the average person browsing the web.
“Their intention is clear: avoid detection and make it difficult for defenders to protect against,” Lumen’s report concludes.
“KadNap’s bots are sold through Doppelganger, a service whose users leverage these hijacked devices for a range of malicious purposes, including brute-force attacks and highly targeted exploitation campaigns.
“As a result, every IP address associated with this botnet represents a significant, persistent risk to organizations and individuals alike.”


.jpeg?width=1200&height=800&crop=1200:800)
